Z Trek: The Alan Zeichick Weblog

Why you need Security & Systems Operations – SysSecOps
SysSecOps is a new phrase, still unseen by many IT and security administrators – however it’s being discussed within the market, by analysts, and at technical conferences. SysSecOps, or Systems & Security Operations, describes the practice…

Forget Harbor Freight, you want Hazard Fraught Tools
Low-Quality Tools at Ridiculous Prices!
Don’t click on “must validate account” email scams!
This fake message from “Netflix” almost got me, and as you know I’m quite skeptical about these things. Unlike most scams, it’s neatly formatted and well-written. And because my family has a Netflix account, it didn’t seem completely…

A great scam says that the question is you, the answer is God
This scam is comically bad, yet who knows if anyone fell for it? This is exactly how the mail came through. I’m leaving in the email addresses, well, just because.
I love the question and answers below, and the attention to detail — even…

Celebrate the Shehecheyanu Moments and give thanks
On this day before Thanksgiving (a U.S. holiday), let me share the concept of Shehecheyanu Moments.
The Shehecheyanu is a prayer of thankfulness. Many Jews say the prayer immediately after the first time you do or experience something new…

Four tactics to prevent and manage ransomware
Ransomware is genuine, and is threatening individuals, services, schools, medical facilities, governments – and there’s no indication that ransomware is stopping. In fact, it’s probably increasing. Why? Let’s be honest: Ransomware is…
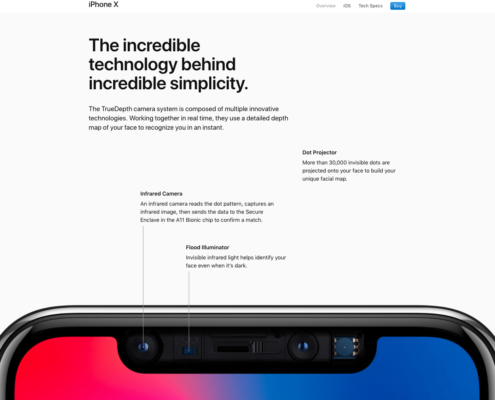
Passwords? Fingerprints? Face recognition? It’s all questionable.
I unlock my smartphone with a fingerprint, which is pretty secure. Owners of the new Apple iPhone X unlock theirs with their faces – which is reported to be hackable with a mask. My tablet is unlocked with a six-digit numerical code, which…
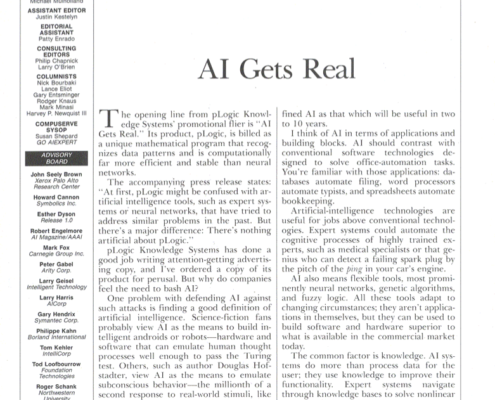
Artificial Intelligence Got Real – In 1991
AI is an emerging technology – always, has been always will be. Back in the early 1990s, I was editor of AI Expert Magazine. Looking for something else in my archives, I found this editorial, dated February 1991.
What do you think? Is AI…
Be wary of cloud download links, such as from Dropbox, Google Drive or Microsoft OneDrive
A lot of people share files with friends or colleagues by uploading them to cloud storage and sending an access link. I do this myself, sharing folders, documents or photo collections.
Malicious scammers can do the same thing. It’s…

AI-driven network scanning is the secret to effective mobile security
The secret sauce is AI-based zero packet inspection. That’s how to secure mobile users, and their personal data and employers’ data.
Let’s back up a step. Mobile devices are increasingly under attack, from malicious apps, from rogue…

How AI is changing the role of cybersecurity – and of cybersecurity experts
In The Terminator, the Skynet artificial intelligence was turned on to track down hacking a military computer network. Turns out the hacker was Skynet itself. Is there a lesson there? Could AI turn against us, especially as it relates to the…

Here’s how to fight and defeat the new hackers
Let’s talk about hackers, not through the eyes of the tech industry but through the eyes of current and former U.S. law enforcement officials. It’s their job to run those people down and throw them in jail.
The Federal Bureau of Investigation
MK…

Forget the IoT: It’s all about the Industrial IoT
Smart televisions, talking home assistants, consumer wearables – that’s not the real story of the Internet of Things. While those are fun and get great stories on blogs and morning news reports, the real IoT is the Industrial IoT. That’s…

Why you should care about serverless computing
The bad news: There are servers used in serverless computing. Real servers, with whirring fans and lots of blinking lights, installed in racks inside data centers inside the enterprise or up in the cloud.
The good news: You don’t need to…

Too long: The delays between cyberattacks and their discovery and disclosure
Critical information about 46 million Malaysians were leaked online onto the Dark Web. The stolen data included mobile phone numbers from telcos and mobile virtual network operators (MVNOs), prepaid phone numbers, customers details including…

Taking a KRACK at an Internet of Things vulnerability
It’s always nice when a friend is quoted in an article. In this case, it’s one of my dearest and closest, John Romkey, founder of FTP Software. The story is, “The Internet Of Things Just Got Even More Unsafe To Use,” by Harold Stark,…
It’s a bot, bot, bot world: The new battle for enterprise cybersecurity
Humans can’t keep up. At least, not when it comes to meeting the rapidly expanding challenges inherent to enterprise cybersecurity. There are too many devices, too many applications, too many users, and too many megabytes of log files for…

An heiress wants to give you money – well, a scammer, not an heiress
Here’s a classic example of a scam that cites a news story as validation that the claim is authentic, or at least credible. It’s not. Despite the scammer’s citing a famous story about an heiress bequeathing a fortune, that’s no proof…

No pastrami sandwich or guinea pig emoji in iOS 11.1, dammit
Still no pastrami sandwich. Still no guinea pig. What’s the deal with the cigarette?
I installed iOS 11.1 yesterday, tantalized by Apple’s boasting of tons of new emoji. Confession: Emoji are great fun. Guess what I looked for right after…

Backlinko has a great guide to search engine optimize (SEO)
You want to read Backlinko’s “The Definitive Guide To SEO In 2018.” Backlinko is an SEO consultancy founded by Brian Dean. The “Definitive Guide” is a cheerfully illustrated infographic – a lengthy infographic – broken up into…
Well, what the heck, I went and did my Halloween best
Our family’s Halloween tradition: Watch “The Nightmare Before Christmas,” singing along with all the songs. Great songs!
I must make my usual complaints about this Disney movie. The biggest is there’s only one major female character…

Seeing the face of God in an eclipse
What happens when the sun goes disappears during the daytime? Rabbi Margaret Frisch Klein, of Congregation Kneseth Israel in Elgin, Illinois, wrote in her Energizer Rabbi blog on Aug. 22, 2017, just before the solar eclipse:
The sun is going…
The same coding bugs cause the same security vulnerabilities, year after year
Software developers and testers must be sick of hearing security nuts rant, "Beware SQL injection! Monitor for cross-site scripting! Watch for hijacked session credentials!" I suspect the developers tune us out. Why? Because we've been raving…

Patches are security low-hanging fruit — but there’s too much of it
Apply patches. Apply updates. Those are considered to be among the lowest-hanging of the low-hanging fruit for IT cybersecurity. When commercial products release patches, download and install the code right away. When open-source projects disclose…

Buying a “Best in Business” award?
You can call me Ray, or you can call me Jay, or you can call me Johnny or you can call me Sonny, or you can call me RayJay, or you can call me RJ… but ya doesn’t hafta call me Johnson.
That’s a great line from the comedian Bill Saluga…

A link to a famous person’s Wikipedia page means nothing
This is a common scam: The scammer pretends to be a famous person, and links to the bio or a story about that person. That means nothing. A person wants to share some gold with you, and links to a BBC story about a battle in Iraq or Afghanistan.…
Managing the impact of open source software on data centers
Open source software (OSS) offers many benefits for organizations large and small—not the least of which is the price tag, which is often zero. Zip. Nada. Free-as-in-beer. Beyond that compelling price tag, what you often get with OSS is a…

My 10 favorite Star Trek episodes
For no particular reason, and in alphabetical order, my favorite episodes from the original Star Trek, aka, The Original Series.
Arena
Kirk and the captain of the Gorn ship are told to fight to the death as proxies for a space battle,…

Lift-and-shift vs building native cloud apps: Two Ways, Three Tracks
Those are two popular ways of migrating enterprise assets to the cloud:
Write new cloud-native applications.
Lift-and-shift existing data center applications to the cloud.
Gartner’s definition: “Lift-and-shift means that workloads…
Hurray, Mr. Bill Gates wants to give me five million dollars!
I can’t believe my luck – Microsoft co-founder Bill Gates wants to give me $5 million. Hurray! And not only that, he’s contacting me from an email address at Nelson Mandela University in South Africa. It’s also a shame to learn that…
