Low-Quality Tools at Ridiculous Prices!




Low-Quality Tools at Ridiculous Prices!




This fake message from “Netflix” almost got me, and as you know I’m quite skeptical about these things. Unlike most scams, it’s neatly formatted and well-written. And because my family has a Netflix account, it didn’t seem completely unreasonable.
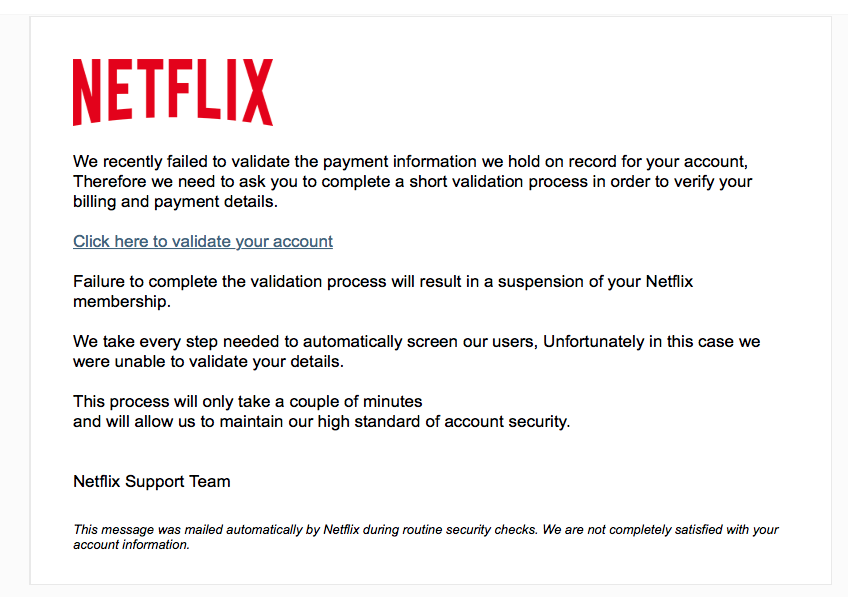
What gave it away? First, vendors don’t sent out emails demanding to “validate” information or your account will be closed or suspended. They simply don’t.
Second, looking at the email’s invisible details gave away the scam:
When you get emails that seem plausible, hover your mouse over the links, and see where they go. Don’t click. If the link destinations smell wrong, the message is a scam. Plain and simple. Don’t respond, don’t click on anything in such messages; simply delete them.
 This scam is comically bad, yet who knows if anyone fell for it? This is exactly how the mail came through. I’m leaving in the email addresses, well, just because.
This scam is comically bad, yet who knows if anyone fell for it? This is exactly how the mail came through. I’m leaving in the email addresses, well, just because.
I love the question and answers below, and the attention to detail — even the FedEx address is fake. Be sure to tell her your nearest airport! Needless to say, delete messages like this, don’t reply to them.
From: ZENITH BANK ATM CARD PAYMENT email hidden; JavaScript is required
Subject: ZENITH BANK ATM CARD PAYMENT
Date: November 21, 2017 at 1:46:04 PM MST
To: Undisclosed recipients
Reply-To: email hidden; JavaScript is requiredZENITH BANK ATM CARD PAYMENT
RE: YOU’RE PAYMENT NOTIFICATIONFrom: Mrs.Lizzy Ben
ATM CARD Remittance Manager
Zenith Bank of Nigeria.
Email email hidden; JavaScript is requiredAttention Beneficiary,
I am Mrs.Lizzy Ben, the new account audit of Zenith Bank Plc Nigeria and i am writing to notify you of a payment file containing an ATM card which has been issued out to you by the Federal Ministry of Finance injunction with the United Nation/International Monetary Fund (IMF).
I am new here in this office and i have orders from the entire government of the Federal republic of Nigeria to contact beneficiaries and make sure they receive their ATM cards if it’s still in custody of this bank. Can you kindly let us know the reason of your delay concerning the Delivery of your ATM CARD? Why do you decide to abandon your ATM CARD? Worth of $8.5million USD with us, if you fail to contact us on or Before 48 hours or else we shall cancel the delivery of your ATM CARD and return your fund to government reserve account, your delivery Process had been done.
If you are ready to receive your ATM card then make sure to contact the courier company which is in charge of making delivery of parcel. I have made several inquiries on various delivery companies and the only fee you have to pay for the delivery is $155.00 usd which covers the delivery to your doorstep.
This is the cheapest i could find and I was made to understand it takes just 3 days to get your package to your residence. On receipt of the required payment a tracking number will be sent to you to enable you track your package till it gets to your residence.
So, contact the director of the delivery company with the following details, so contact Him and also make sure that you send them the above Mentioned fee through western Union or Money Gram For the immediate procedure of your ATM CARD delivery to avoid any delay.
RECEIVERS NAME:
LOCATION: 45 ALLEN AVE,LAGOS NIGERIA
QUESTION: YOU?
ANSWER: GOD
AMOUNT: $155.00USD
MTCN:………
Senders Full Name:……….
Home/Office Address:……..
Cell/Mobile Phone Numbers:………
Nearest Air Port:……….Name of Delivery Company: FEDEX DELIVERY COURIER COMPANY, LAGOS BRANCH.
Director in Charge: MR.SAM BROWN
Contact Email: email hidden; JavaScript is required
Contact Cell/Mobile Number: +234-8-125-120-544
Contact the delivery company personnel as soon as possible or risk loosing the ATM.Yours Sincerely,
Mrs.Lizzy Ben.
Zenith Bank ATM MASTER CARD DPT.
E-MAIL:zenithbankplc860@gmail.com
 On this day before Thanksgiving (a U.S. holiday), let me share the concept of Shehecheyanu Moments.
On this day before Thanksgiving (a U.S. holiday), let me share the concept of Shehecheyanu Moments.
The Shehecheyanu is a prayer of thankfulness. Many Jews say the prayer immediately after the first time you do or experience something new and wonderful, or right after you experience it for the first time in a long time.
In my family, we call such occasions Shehecheyanu Moments. In English, the prayer roughly translates to, “Thank you, God, for giving me life, sustaining me, and letting me reach this season.”
Every single day, you do or see something new or new-ish, maybe sacred, maybe part of your daily life.
It might be seeing a new rainbow. It might be welcoming your adult son home after six months away. It might starting a job or landing a client. It might be installing a new battery and having the car start right up. It might be hearing goldfinches sing after a few months’ absence. It might be watching a baby bunny hop across the garden. It might be tasting an interesting wine varietal or flavor of herbal tea. It might be hugging friends this Thanksgiving you haven’t hugged since last Thanksgiving.
Treasure and acknowledge (even if only to yourself) those Shehecheyanu Moments. They truly sustain us, and teach that each and every day, life fills us with joy and blessings.
Happy Thanksgiving!
 Ransomware is genuine, and is threatening individuals, services, schools, medical facilities, governments – and there’s no indication that ransomware is stopping. In fact, it’s probably increasing. Why? Let’s be honest: Ransomware is probably the single most efficient attack that hackers have ever created. Anybody can develop ransomware utilizing easily available tools; any cash received is likely in untraceable Bitcoin; and if something goes wrong with decrypting someone’s disk drive, the hacker isn’t impacted.
Ransomware is genuine, and is threatening individuals, services, schools, medical facilities, governments – and there’s no indication that ransomware is stopping. In fact, it’s probably increasing. Why? Let’s be honest: Ransomware is probably the single most efficient attack that hackers have ever created. Anybody can develop ransomware utilizing easily available tools; any cash received is likely in untraceable Bitcoin; and if something goes wrong with decrypting someone’s disk drive, the hacker isn’t impacted.
A business is hit with ransomware every 40 seconds, according to some sources, and 60% of all malware were ransomware. It strikes all sectors. No industry is safe. And with the increase of RaaS (Ransomware-as-a-Service) it’s going to get worse.
Fortunately: We can fight back. Here’s a 4 step fight plan.
By the way, businesses need tools to discover, determine, and avoid malware like ransomware from dispersing. This needs continuous visibility and reporting of what’s taking place in the environment – consisting of “zero day” attacks that have not been seen before. Part of that is keeping an eye on end points, from the smart phone to the PC to the server to the cloud, to make sure that endpoints are up-to-date and secure, which no unexpected changes have been made to their underlying configuration. That way, if a machine is contaminated by ransomware or other malware, the breach can be discovered quickly, and the device separated and closed down pending forensics and healing. If an end point is breached, quick containment is critical.
Read more in my guest story for Chuck Leaver’s blog, “Prevent And Manage Ransomware With These 4 Steps.”
 I unlock my smartphone with a fingerprint, which is pretty secure. Owners of the new Apple iPhone X unlock theirs with their faces – which is reported to be hackable with a mask. My tablet is unlocked with a six-digit numerical code, which is better than four digits or a pattern. I log into my laptop with an alphanumeric password. Many online services, including banks and SaaS applications, require their own passwords.
I unlock my smartphone with a fingerprint, which is pretty secure. Owners of the new Apple iPhone X unlock theirs with their faces – which is reported to be hackable with a mask. My tablet is unlocked with a six-digit numerical code, which is better than four digits or a pattern. I log into my laptop with an alphanumeric password. Many online services, including banks and SaaS applications, require their own passwords.
It’s a mess! Not the least because lazy humans tend to reuse passwords, so that if a username and password for one service is stolen, criminals can try using that same combination on other services. Hackers steal your email and password from some insecure e-commerce site’s breach? They’ll try that same ID and password on Facebook, LinkedIn, eBay, Amazon, Walmart.com, Gmail, Office 365, Citibank, Fidelity, Schwab… you get the idea.
Two more weaknesses: Most people don’t change their passwords frequently, and the passwords that they choose are barely more secure than ABCD?1234. And while biometrics are good, they’re not always sufficient. Yes, my smartphone has a fingerprint sensor, but my laptop doesn’t. Sure, companies can add on such technology, but it’s a kludge. It’s not a standard, and certainly I can’t log into my Amazon.com account with a fingerprint swipe.
The 2017 Verizon Data Breach Report reports that 81% of hacking-related breaches leverage either stolen or weak passwords. That’s the single biggest tactic used in breaches – followed by actual hacking, at 62%, and malware, at 51%.
To quote from the report: “… if you are relying on username/email address and password, you are rolling the dice as far as password re-usage from other breaches or malware on your customers’ devices are concerned.” About retailers specifically — which is where we see a lot of breaches — Verizon writes: “Their business is their web presence and thus the web application is the prime target of compromise to harvest data, frequently some combination of usernames, passwords (sometimes encrypted, sometimes not), and email addresses.”
By the way, I am dismayed by the common use of a person’s email address instead of a unique login name by many retailers and online services. That reduces the bits of data that hackers or criminals need. It’s pretty easy to figure out my email address, which means that to get into my bank account, all you need is to guess or steal my password. But if my login name was a separate thing, like WeinerDogFancier, you’d have to know that andfind my password. On the other hand, using the email address makes things easier for programmers, and presumably for users as well. As usual, convenience beats security.
The Deloitte breach, which was discovered in March 2017, succeeded because an administrator account had basically unfettered access to everything. And that account wasn’t secured by two-factor authentication. There were apparently no secondary password protecting critical assets, even from an authenticated user.
As the Guardian wrote in “Deloitte hit by cyber-attack revealing clients’ secret emails,”
The hacker compromised the firm’s global email server through an “administrator’s account” that, in theory, gave them privileged, unrestricted “access to all areas”. The account required only a single password and did not have “two-step“ verification, sources said. Emails to and from Deloitte’s 244,000 staff were stored in the Azure cloud service, which was provided by Microsoft. This is Microsoft’s equivalent to Amazon Web Service and Google’s Cloud Platform. In addition to emails, the Guardian understands the hackers had potential access to usernames, passwords, IP addresses, architectural diagrams for businesses and health information. Some emails had attachments with sensitive security and design details.
There are no universal solutions to the password scourge. However, there are some best practices:
You might enjoy this riff on passwords by Jeff Atwood in his blog, Coding Horror. Be sure to read the comments.
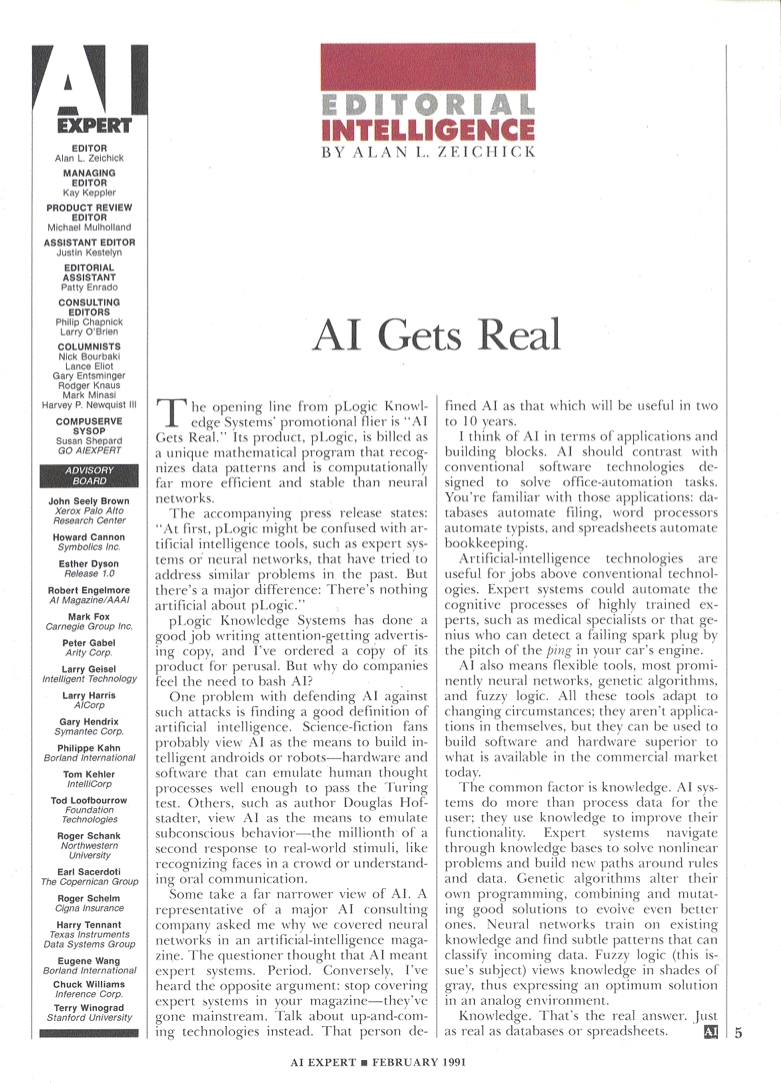
AI is an emerging technology – always, has been always will be. Back in the early 1990s, I was editor of AI Expert Magazine. Looking for something else in my archives, I found this editorial, dated February 1991.
What do you think? Is AI real yet?

A lot of people share files with friends or colleagues by uploading them to cloud storage and sending an access link. I do this myself, sharing folders, documents or photo collections.
Malicious scammers can do the same thing. It’s a great technique for them, because the email itself has no attachments, and thus won’t set off anti-virus or anti-malware filters. However, once you click on the link, wham. You’ve just downloaded malware, like an infected Word doc or PDF. Alternatively, you may have been directed to a website that automatically loads malware or does phishing to steal your personal info.
Here is a sample of this type of email. This email’s link doesn’t go to a document – it goes to a malware-packed website. Of course, the lousy grammar helps us see that this email is a scam, but the scammers are getting better at this sort of thing.
If you receive an email from someone you don’t know, and it asks you to click a link or open an attachment, delete the email right away. And if you receive an email like this from someone you do know, and you weren’t expecting to receive such a message, verify with them that they actually sent it before proceeding. Ask by phone, or text, or by sending a new message – not by replying to the possible scam message. Don’t be fooled!
One final note: The scam says, “This message has been scanned for viruses and dangerous content by MailScanner, and is believed to be clean.” Uh, no. Such claims mean nothing. Anyone can type those words, or insert a logo.
 The secret sauce is AI-based zero packet inspection. That’s how to secure mobile users, and their personal data and employers’ data.
The secret sauce is AI-based zero packet inspection. That’s how to secure mobile users, and their personal data and employers’ data.
Let’s back up a step. Mobile devices are increasingly under attack, from malicious apps, from rogue emails, from adware, and from network traffic. Worse, that network traffic can come from any number of sources, including cellular data, WiFi, even Bluetooth. Users want their devices to be safe and secure. But how, if the network traffic can’t be trusted?
The best approach around is AI-based zero packet inspection (ZPI). It all starts with data. Tons of training data, used to train a machine learning algorithm to recognize patterns that indicate whether a device is performing normally – or if it’s under attack. Machine learning refers to a number of advanced AI algorithms that can study streams of data, rapidly and accurately detect patterns in that data, and from those patterns, sort the data into different categories.
The Zimperium z9 engine, as an example, works with machine learning to train against a number of test cases (on both iOS and Android devices) that represent known patterns of safe and not-safe traffic. We call those patterns zero-packet inspection in that the objective is not to look at the contents of the network packets but to scan the lower-level underlying traffic patterns at the network level, such as IP, TCP, UDP and ARP scans.
If you’re not familiar with those terms, suffice it to say that at the network level, the traffic is focused on delivering data to a specific device, and then within that device, making sure it gets to the right application. Think of it as being like an envelope going to a big business – it has the business name, street address, and department/mail stop. The machine learning algorithms look at patterns at that level, rather than examining the contents of the envelope. This makes the scans very fast and accurate.
Read more in my new essay for Security Brief Europe, “Opinion: Mobile security starts with a powerful AI-based scanning engine.”
In The Terminator, the Skynet artificial intelligence was turned on to track down hacking a military computer network. Turns out the hacker was Skynet itself. Is there a lesson there? Could AI turn against us, especially as it relates to the security domain?

That was one of the points I made while moderating a discussion of cybersecurity and AI back in October 2017. Here’s the start of a blog post written by my friend Tami Casey about the panel:
Mention artificial intelligence (AI) and security and a lot of people think of Skynet from The Terminator movies. Sure enough, at a recent Bay Area Cyber Security Meetup group panel on AI and machine learning, it was moderator Alan Zeichick – technology analyst, journalist and speaker – who first brought it up. But that wasn’t the only lively discussion during the panel, which focused on AI and cybersecurity.
I found two areas of discussion particularly interesting, which drew varying opinions from the panelists. One, around the topic of AI eliminating jobs and thoughts on how AI may change a security practitioner’s job, and two, about the possibility that AI could be misused or perhaps used by malicious actors with unintended negative consequences.
It was a great panel. I enjoyed working with the Meetup folks, and the participants: Allison Miller (Google), Ali Mesdaq (Proofpoint), Terry Ray (Imperva), Randy Dean (Launchpad.ai & Fellowship.ai).
You can read the rest of Tami’s blog here, and also watch a video of the panel.
 Let’s talk about hackers, not through the eyes of the tech industry but through the eyes of current and former U.S. law enforcement officials. It’s their job to run those people down and throw them in jail.
Let’s talk about hackers, not through the eyes of the tech industry but through the eyes of current and former U.S. law enforcement officials. It’s their job to run those people down and throw them in jail.
MK Palmore is an Information Security Risk Management Executive with the FBI’s Cyber Branch in San Francisco. He runs the cyber-security teams assigned to the San Francisco division of the FBI. “My teams here in San Francisco typically play some part in the investigations, where our role is to identify, define attribution, and get those folks into the U.S. Justice system.”
“The FBI is 35,000-plus personnel, U.S.-based, and part of the Federal law enforcement community,” says Palmore. “There are 56 different field offices throughout the United States of America, but we also have an international presence in more than 62 cities throughout the world. A large majority of those cities contain personnel that are assigned there specifically for responsibilities in the cyber-security realm, and often-times are there to establish relationships with our counterparts in those countries, but also to establish relationships with some of the international companies, and folks that are raising their profile as it relates to international cyber-security issues.”
It’s not really a secret: In 1865, the Secret Service was created by Congress to primarily suppress counterfeit currency. “Counterfeit currency represented greater than 50% of all the currency in the United States at that time, and that was why the Agency was created,” explained Dr. Ronald Layton, Deputy Assistant Director U.S. Secret Service. “The Secret Service has gone from suppressing counterfeit currency, or economic, or what we used to refer to as paper crimes, to plastic, meaning credit cards. So, we’ve had a progression, from paper, to plastic, to digital crimes, which is where we are today,” he continued.
“I found a giant hole in the way that private sector businesses are handling their security,” said Michael Levin. “They forgot one very important thing. They forgot to train their people what to do. I work with organizations to try to educate people — we’re not doing a very good job of protecting ourselves. “
A leading expert in cyber-security, Levin is Former Deputy Director, U.S. Department of Homeland Security’s National Cyber-Security Division. He retired from the government a few years ago, and is now CEO & Founder of the Center for Information Security Awareness.
“When I retired from the government, I discovered something,” he continued. “We’re not protecting our own personal data – so, everybody has a role to play in protecting their personal data, and their family’s data. We’re not protecting our business data. Then, we’re not protecting our country’s data, and there’s nation states, and organized crime groups, and activists, that are coming after us on a daily basis.”
There are essentially four groups of cyber-threat activists that we need to be concerned with, explained the FBI’s Palmore. “I break them down as financially-motivated criminal intrusion, threat actors, nation states, hacktivists, and then those security incidents caused by what we call the insider threat. The most prevalent of the four groups, and the most impactful, typically, are those motivated by financial concerns.”
“We’re talking about a global landscape, and the barrier to entry for most financially-motivated cyber-threat actors is extremely low,” Palmore continued. “In terms of looking at who these folks are, and in terms of who’s on the other end of the keyboard, we’re typically talking about mostly male threat actors, sometimes between the ages of, say, 14 and 32 years old. We’ve seen them as young as 14.”
Criminals? Nation states? Hacktivists? Insiders? While that matters to law enforcement, it shouldn’t to individuals and enterprise, said CIFSA’s Levin. “For most people, they don’t care if it’s a nation state. They just want to stop the bleeding. They don’t care if it’s a hacktivist, they just want to get their site back up. They don’t care who it is. They just start trying to fix the problem, because it means their business is being attacked, or they’re having some sort of a failure, or they’re losing data. They’re worried about it. So, from a private sector company’s business, they may not care.”
However, “Law enforcement cares, because they want to try to catch the bad guy. But for the private sector is, the goal is to harden the target,” points out Levin. “Many of these attacks are, you know, no different from a car break-in. A guy breaking into cars is going to try the handle first before he breaks the window, and that’s what we see with a lot of these hackers. Doesn’t matter if they’re nation states, it doesn’t matter if they’re script kiddies. It doesn’t matter to what level of the sophistication. They’re going to look for the open doors first.”
The Secret Service focuses almost exclusively about folks trying to steal money. “Several decades ago, there was a famous United States bank robber named Willie Sutton,” said Layton. “Willie Sutton was asked, why do you rob banks? ‘Because that’s where the money is.’ Those are the people that we deal with.”
Layton explained that the Secret Service has about a 25-year history of investigating electronic crimes. The first electronic crimes taskforce was established in New York City 25 years ago. “What has changed in the last five or 10 years? The groups worked in isolation. What’s different? It’s one thing: They all know each other. They all are collaborative. They all use Russian as a communications modality to talk to one another in an encrypted fashion. That’s what’s different, and that represents a challenge for all of us.”
Palmore, Levin, and Layton have excellent, practical advice on how businesses and individuals can protect themselves from cybercrime. They also explain how law enforcement can help. Read more in my article for Upgrade Magazine, “The new hacker — Who are they, what they want, how to defeat them.”
 Smart televisions, talking home assistants, consumer wearables – that’s not the real story of the Internet of Things. While those are fun and get great stories on blogs and morning news reports, the real IoT is the Industrial IoT. That’s where businesses will truly be transformed, with intelligent, connected devices working together to improve services, reduce friction, and disrupt everything. Everything.
Smart televisions, talking home assistants, consumer wearables – that’s not the real story of the Internet of Things. While those are fun and get great stories on blogs and morning news reports, the real IoT is the Industrial IoT. That’s where businesses will truly be transformed, with intelligent, connected devices working together to improve services, reduce friction, and disrupt everything. Everything.
According to Grand View Research, the Industrial IoT (IIoT) market will be $933.62 billion by 2025. “The ability of IoT to reduce costs has been the prime factor for its adoption in the industrial sector. However, several significant investment incentives, such as increased productivity, process automation, and time-to-market, have also been boosting this adoption. The falling prices of sensors have reduced the overall cost associated with data collection and analytics,” says the report.
The report continues,
An emerging trend among enterprises worldwide is the transformation of technical focus to improving connectivity in order to undertake data collection with the right security measures in place and with improved connections to the cloud. The emergence of low-power hardware devices, cloud integration, big data analytics, robotics & automation, and smart sensors are also driving IIoT market growth.
Markets & Markets predicts that IIoT will be worth $195.47 billion by 2022. The company says,
A key influencing factor for the growth of the IIoT market is the need to implement predictive maintenance techniques in industrial equipment to monitor their health and avoid unscheduled downtimes in the production cycle. Factors which driving the IIoT market include technological advancements in semiconductor and electronics industry and evolution of cloud computing technologies.
The manufacturing vertical is witnessing a transformation through the implementation of the smart factory concept and factory automation technologies. Government initiatives such as Industrie 4.0 in Germany and Plan Industriel in France are expected to promote the implementation of the IIoT solutions in Europe. Moreover, leading countries in the manufacturing vertical such as U.S., China, and India are expected to further expand their manufacturing industries and deploy smart manufacturing technologies to increase this the contribution of this vertical to their national GDPs.
The IIoT market for camera systems is expected to grow at the highest rate between 2016 and 2022. Camera systems are mainly used in the retail and transportation verticals. The need of security and surveillance in these sectors is the key reason for the high growth rate of the market for camera systems. In the retail sector, the camera systems are used for capturing customer behavior, moment tracking, people counting, and heat mapping. The benefits of installation of surveillance systems include the safety at the workplace, and the prevention of theft and other losses, sweet hearting, and other retail crimes. Video analytics plays a vital role for security purpose in various areas in transportation sector including airports, railway stations, and large public places. Also, intelligent camera systems are used for traffic monitoring, and incident detection and reporting.
The huge research firm Accenture says that the IIoT will add $14.2 trillion to the global economy by 2030. That’s not talking about the size of the market, but the overall lift that IIoT will have. By any measure, that’s staggering. Accenture reports,
Today, the IIoT is helping to improve productivity, reduce operating costs and enhance worker safety. For example, in the petroleum industry, wearable devices sense dangerous chemicals and unmanned aerial vehicles can inspect remote pipelines.
However, the longer-term economic and employment potential will require companies to establish entirely new product and service hybrids that disrupt their own markets and generate fresh revenue streams. Many of these will underpin the emergence of the “outcome economy,” where organizations shift from selling products to delivering measurable outcomes. These may range from guaranteed energy savings in commercial buildings to guaranteed crop yields in a specific parcel of farmland.
The IIoT is going to have huge impact. But it hasn’t yet, not on any large scale. As Accenture says,
When Accenture surveyed more than 1,400 C-suite decision makers—including 736 CEOs—from some of the world’s largest companies, the vast majority (84 percent) believe their organizations have the capability to create new, service-based income streams from the IIoT.
But scratch beneath the surface and the gloss comes off. Seventy-three percent confess that their companies have yet to make any concrete progress. Just 7 percent have developed a comprehensive strategy with investments to match.
Challenge and opportunity: That’s the Industrial Internet of Things. Watch this space.
 The bad news: There are servers used in serverless computing. Real servers, with whirring fans and lots of blinking lights, installed in racks inside data centers inside the enterprise or up in the cloud.
The bad news: There are servers used in serverless computing. Real servers, with whirring fans and lots of blinking lights, installed in racks inside data centers inside the enterprise or up in the cloud.
The good news: You don’t need to think about those servers in order to use their functionality to write and deploy enterprise software. Your IT administrators don’t need to provision or maintain those servers, or think about their processing power, memory, storage, or underlying software infrastructure. It’s all invisible, abstracted away.
The whole point of serverless computing is that there are small blocks of code that do one thing very efficiently. Those blocks of code are designed to run in containers so that they are scalable, easy to deploy, and can run in basically any computing environment. The open Docker platform has become the de facto industry standard for containers, and as a general rule, developers are seeing the benefits of writing code that target Docker containers, instead of, say, Windows servers or Red Hat Linux servers or SuSE Linux servers, or any specific run-time environment. Docker can be hosted in a data center or in the cloud, and containers can be easily moved from one Docker host to another, adding to its appeal.
Currently, applications written for Docker containers still need to be managed by enterprise IT developers or administrators. That means deciding where to create the containers, ensuring that the container has sufficient resources (like memory and processing power) for the application, actually installing the application into the container, running/monitoring the application while it’s running, and then adding more resources if required. Helping do that is Kubernetes, an open container management and orchestration system for Docker. So while containers greatly assist developers and admins in creating portable code, the containers still need to be managed.
That’s where serverless comes in. Developers write their bits of code (such as to read or write from a database, or encrypt/decrypt data, or search the Internet, or authenticate users, or to format output) to run in a Docker container. However, instead of deploying directly to Docker, or using Kubernetes to handle deployment, they write their code as a function, and then deploy that function onto a serverless platform, like the new Fn project. Other applications can call that function (perhaps using a RESTful API) to do the required operation, and the serverless platform then takes care of everything else automatically behind the scenes, running the code when needed, idling it when not needed.
Read my essay, “Serverless Computing: What It Is, Why You Should Care,” to find out more.
 Critical information about 46 million Malaysians were leaked online onto the Dark Web. The stolen data included mobile phone numbers from telcos and mobile virtual network operators (MVNOs), prepaid phone numbers, customers details including physical addresses – and even the unique IMEI and IMSI registration numbers associated with SIM cards.
Critical information about 46 million Malaysians were leaked online onto the Dark Web. The stolen data included mobile phone numbers from telcos and mobile virtual network operators (MVNOs), prepaid phone numbers, customers details including physical addresses – and even the unique IMEI and IMSI registration numbers associated with SIM cards.
Isolated instance from one rogue carrier? No. The carriers included Altel, Celcom, DiGi, Enabling Asia, Friendimobile, Maxis, MerchantTradeAsia, PLDT, RedTone, TuneTalk, Umobile and XOX; news about the breach were first published 19 October 2017 by a Malaysian online community.
When did the breach occur? According to lowyat.net, “Time stamps on the files we downloaded indicate the leaked data was last updated between May and July 2014 between the various telcos.”
That’s more than three years between theft of the information and its discovery. We have no idea if the carriers had already discovered the losses, and chose not to disclose the breaches.
A huge delay between a breach and its disclosure is not unusual. Perhaps things will change once the General Data Protection Regulation (GDPR) kicks in next year, when organizations must reveal a breach within three days of discovery. That still leaves the question of discovery. It simply takes too long!
According to Mandiant, the global average dwell time (time between compromise and detection) is 146 days. In some areas, it’s far worse: the EMEA region has a dwell time of 469 days. Research from the Ponemon Institute says that it takes an average of 98 days for financial services companies to detect intrusion on their networks, and 197 days in retail. It’s not surprising that the financial services folks do a better job – but three months seems like a very long time.
An article headline from InfoSecurity Magazine says it all: “Hackers Spend 200+ Days Inside Systems Before Discovery.” Verizon’s Data Breach Investigations Report for 2017 has some depressing news: “Breach timelines continue to paint a rather dismal picture — with time-to-compromise being only seconds, time-to-exfiltration taking days, and times to discovery and containment staying firmly in the months camp. Not surprisingly, fraud detection was the most prominent discovery method, accounting for 85% of all breaches, followed by law enforcement which was seen in 4% of cases.”
There are two relevant statistics. The first is time-to-discovery, and the other is time-to-disclosure, whether to regulators or customers.
What’s needed are comprehensive endpoint monitoring capabilities, coupled with excellent threat intelligence and real-time analytics driven by machine learning. Nothing else can correlate huge quantities of data from such widely disparate sources, and hope to discover outliers based on patterns.
Discovery and containment takes months, says Verizon. You can’t have containment without discovery. With current methods, we’ve seen that discovery takes months or years, if it’s every detected at all. Endpoint monitoring technology, when coupled with machine learning — and with 24×7 managed security software providers — can reduce that to seconds or minutes.
There is no excuse for breaches staying hidden for three years or longer. None. That’s no way to run a business.
 It’s always nice when a friend is quoted in an article. In this case, it’s one of my dearest and closest, John Romkey, founder of FTP Software. The story is, “The Internet Of Things Just Got Even More Unsafe To Use,” by Harold Stark, and published on Forbes.com.
It’s always nice when a friend is quoted in an article. In this case, it’s one of my dearest and closest, John Romkey, founder of FTP Software. The story is, “The Internet Of Things Just Got Even More Unsafe To Use,” by Harold Stark, and published on Forbes.com.
The story talks about a serious vulnerability in the Internet of Things:
Mathy Vanhoef, Security Researcher at KU Leuven, made headlines last week with a blog where he described this strange new vulnerability that had the potential to affect every device that has ever been on a wi-fi network all at once. The vulnerability, dubbed KRACK or Key Reinstallation Attack, has a simple way of functioning. WPA2-PSK, the most widely used security protocol used to secure devices and routers connected to a wi-fi network, had a glaring flaw. This flaw, which allows a third-party hacker to trick their way into a device as it connects to a wi-fi network using a password, allows said hacker to access and modify all information available to this device without even being on the network. By interfering with the authorization process that allows a device to connect to a closed wi-fi network, the hacker can do things such as intercept traffic, access stored data and even modify information accessed by the device at the time. So this hacker could tell which websites you like to visit, play that video from your friend’s wedding last month or even infect your device with an unknown malware to cause further damage. Just to be clear, this vulnerability affects any and all devices that can connect to wi-fi networks, regardless of which software it is running.
You should read the whole story, which includes a quote from my friend John, here.
 Humans can’t keep up. At least, not when it comes to meeting the rapidly expanding challenges inherent to enterprise cybersecurity. There are too many devices, too many applications, too many users, and too many megabytes of log files for humans to make sense of it all. Moving forward, effective cybersecurity is going to be a “Battle of the Bots,” or to put it less dramatically, machine versus machine.
Humans can’t keep up. At least, not when it comes to meeting the rapidly expanding challenges inherent to enterprise cybersecurity. There are too many devices, too many applications, too many users, and too many megabytes of log files for humans to make sense of it all. Moving forward, effective cybersecurity is going to be a “Battle of the Bots,” or to put it less dramatically, machine versus machine.
Consider the 2015 breach at the U.S. Government’s Office of Personnel Management (OPM). According to a story in Wired, “The Office of Personnel Management repels 10 million attempted digital intrusions per month—mostly the kinds of port scans and phishing attacks that plague every large-scale Internet presence.” Yet despite sophisticated security mechanisms, hackers managed to steal millions of records on applications for security clearances, personnel files, and even 5.6 digital images of government employee fingerprints. (In August 2017, the FBI arrested a Chinese national in connection with that breach.)
Traditional security measures are often slow, and potentially ineffective. Take the practice of applying patches and updates to address new-found software vulnerabilities. Companies now have too many systems in play for the process of finding and installing patches to be effectively handled manually,
Another practice that can’t be handled manually: Scanning log files to identify abnormalities and outliers in data traffic. While there are many excellent tools for reviewing those files, they are often slow and aren’t good at aggregating lots across disparate silos (such as a firewall, a web application server, and an Active Directory user authentication system). Thus, results may not be comprehensive, patterns may be missed, and results of deep analysis may not be returned in real time.
Read much more about this in my new essay, “Machine Versus Machine: The New Battle For Enterprise Cybersecurity.”
 Here’s a classic example of a scam that cites a news story as validation that the claim is authentic, or at least credible. It’s not. Despite the scammer’s citing a famous story about an heiress bequeathing a fortune, that’s no proof that this is an heiress looking to give her millions to you. Because it ain’t.
Here’s a classic example of a scam that cites a news story as validation that the claim is authentic, or at least credible. It’s not. Despite the scammer’s citing a famous story about an heiress bequeathing a fortune, that’s no proof that this is an heiress looking to give her millions to you. Because it ain’t.
What’s slightly unusual about this one is that there is no separate reply-to address. Usually the scammers send the email from a real person’s hijacked email address (in this case, the from address is an ordinary gmail.com account) . There is generally a separate reply-to address that’s at a questionable domain elsewhere in the world.
In this message, because there’s no separate reply-to address specified, your response goes back to the original gmail.com address. Hard to know if that address really belongs to the scammer, or if the scammer made a mistake in programming the message. The email address is a bunch of random numbers and letters. Either way… it’s a scam.
Don’t be fooled by links to legitimate news stories. They mean nothing. Delete messages like this; don’t reply or click any links.
From: Elaine Bachmann email hidden; JavaScript is required
Subject: Re: Attn Mr. Alan Zeichick
Date: October 29, 2017 at 5:27:38 AM MST
Dearest
I’m Mrs. Elaine Bachmann from Switzerland once married to Mr. Heinz Bachmann a fellow Swiss. We were married for twenty years without a child. My late husband were dealing mainly in oil in Saudi Arabia before he met his on timing death in a plane crash celebrating his business associate birth-day April 28th 2012.
After the above sad day in my life, I then suffered Oesophageal cancer disease in 2016, and now that the battle is coming to an end due to what my doctor admitted I had just few weeks to live, I’m sadden but happy for the life spent. Now that am about to end the race like this without a child and in contrast to how my family members & friends completely treated me during horrible moment in my life? I decided reaching out to a total stranger in your person to carried out humanitarian work in my memories after coming across a news of 99 years old woman whom secretly donated her fortune prior to her death, you can check below links for details.
http://www.aol.com/article/2014/10/29/standard-oil-heiress-leaves-former-school-40-million/20985809
When my husband was alive, he deposited the sum of $8 Million US Dollars (Eight Million US dollars) in a Security/Finance Company. Presently, this asset is still with the holding firm. With my health situation that i can’t do it myself, I therefore called upon you to accept this donation by using these funds assisting orphans and widows. Late Ms. Ruth Bedford’s Bequeath $40 Million donation had indeed inspired me reaching out to you as a reliable/trustworthy person i can entrust with these funds. I strongly believes God has answered my wish for the needy through you by not betraying my confidence in you.
Please, always be prayerful all through your life by responding for more details.
Yours sister in the Lord,
Elaine Bachmann
 Still no pastrami sandwich. Still no guinea pig. What’s the deal with the cigarette?
Still no pastrami sandwich. Still no guinea pig. What’s the deal with the cigarette?
I installed iOS 11.1 yesterday, tantalized by Apple’s boasting of tons of new emoji. Confession: Emoji are great fun. Guess what I looked for right after the completed software install?
Many of the 190 new emoji are skin-tone variations on new or existing people or body parts. That’s good: Not everyone is yellow, like the Simpsons. (If you don’t count the different skin-tone versions, there are about 70 new graphics.)
New emoji that I like:
What’s still stupidly missing:
I still don’t like the cigarette emoji, but I guess once they added it in 2015, they couldn’t delete it.
Here is a complete list of all the emoji, according to PopSugar. What else is missing?
