L
ong after intruders are removed and public scrutiny has faded, the impacts from a cyberattack can reverberate over a multi-year timeline. Legal costs can cascade as stolen data is leveraged in various ways over time; it can take years to recover pre-incident growth and profitability levels; and brand impact can play out in multiple ways.
That’s from a Deloitte report, “Beneath the surface of a cyberattack: A deeper look at business impacts,” released in late 2016. The report’s contents, and other statements on cyber security from Deloitte, are ironic given the company’s huge breach reported this week.
The big breach
The Deloitte breach was reported on Monday, Sept. 25. It appears to have leaked confidential emails and financial documents of some of its clients. According to the Guardian,
The Guardian understands Deloitte clients across all of these sectors had material in the company email system that was breached. The companies include household names as well as US government departments. So far, six of Deloitte’s clients have been told their information was “impacted” by the hack. Deloitte’s internal review into the incident is ongoing. The Guardian understands Deloitte discovered the hack in March this year, but it is believed the attackers may have had access to its systems since October or November 2016.
The Guardian asserts that hackers gained access to the Deloitte’s global email server via an administrator’s account protected by only a single password. Without two-factor authentication, hackers could gain entry via any computer, as long as they guessed the right password (or obtained it via hacking, malware, or social engineering). The story continues,
In addition to emails, the Guardian understands the hackers had potential access to usernames, passwords, IP addresses, architectural diagrams for businesses and health information. Some emails had attachments with sensitive security and design details.
Okay, the breach was bad. What did Deloitte have to say about these sorts of incidents? Lots.
The Deloitte Cybersecurity Report
In its 2016 report, Deloitte’s researchers pointed to 14 cyberattack impact factors. Half are the directly visible costs of breach incidents; the others which can be more subtle or hidden, and potentially never fully understood.
- The “Above the Surface” incident costs include the expenses of technical investigations, consumer breach notifications, regulatory compliance, attorneys fees and litigation, post-preach customer protection, public relations, and cybersecurity protections.
- Hard to tally are the “Below the Surface” costs of insurance premium increases, increased cost to raise debt, impact of operational disruption/destruction, value of lost contact revenue, devaluation of trade name, loss of intellectual property, and lost value of customer relationship.
As the report says,
Common perceptions about the impact of a cyberattack are typically shaped by what companies are required to report publicly—primarily theft of personally identifiable information (PII), payment data, and personal health information (PHI). Discussions often focus on costs related to customer notification, credit monitoring, and the possibility of legal judgments or regulatory penalties. But especially when PII theft isn’t an attacker’s only objective, the impacts can be even more far-reaching.
Recovery can take a long time, as the Deloitte says:
Beyond the initial incident triage, there are impact management and business recovery stages. These stages involve a wide range of business functions in efforts to rebuild operations, improve cybersecurity, and manage customer and third-party relationships, legal matters, investment decisions, and changes in strategic course.
Indeed, asserts Deloitte in the 2016 report, it can take months or years to repair the damage to the business. That includes redesigning processes and assets, and investing in cyber programs to emerge stronger after the incident. But wait, there’s more.
Intellectual Property and Lawsuits
A big part of the newly reported breach is the loss of intellectual property. That’s not necessarily only Deloitte’s IP, but also the IP of its biggest blue-chip customers. About the loss of IP, the 2016 reports says:
Loss of IP is an intangible cost associated with loss of exclusive control over trade secrets, copyrights, investment plans, and other proprietary and confidential information, which can lead to loss of competitive advantage, loss of revenue, and lasting and potentially irreparable economic damage to the company. Types of IP include, but are not limited to, patents, designs, copyrights, trademarks, and trade secrets.
We’ll see some of those phrases in lawsuits filed by Deloitte’s customers as they try to get a handle on what hackers may have stolen. Oh, about lawsuits, here’s what the Deloitte report says:
Attorney fees and litigation costs can encompass a wide range of legal advisory fees and settlement costs externally imposed and costs associated with legal actions the company may take to defend its interests. Such fees could potentially be offset through the recovery of damages as a result of assertive litigation pursued against an attacker, especially in regards to the theft of IP. However, the recovery could take years to pursue through litigation and may not be ultimately recoverable, even after a positive verdict in favor of the company. Based on our analysis of publicly available data pertaining to recent consumer settlement cases and other legal costs relating to cyber incidents, we observed that, on average, it could cost companies approximately $10 million in attorney fees, potential settlement of loss claims, and other legal matters.
Who wants to bet that the legal costs from this breach will be significantly higher than $10 million?
Stay Vigilant
The back page of Deloitte’s 2016 report says something important:
To grow, streamline, and innovate, many organizations have difficulty keeping pace with the evolution of cyber threats. The traditional discipline of IT security, isolated from a more comprehensive risk-based approach, may no longer be enough to protect you. Through the lens of what’s most important to your organization, you must invest in cost-justified security controls to protect your most important assets, and focus equal or greater effort on gaining more insight into threats, and responding more effectively to reduce their impact. A Secure. Vigilant. Resilient. cyber risk program can help you become more confident in your ability to reap the value of your strategic investments.
Wise words — too bad Deloitte’s email administrators, SOC teams, and risk auditors didn’t heed them. Or read their own report.




 Stupidity. Incompetence. Negligence. The unprecedented huge data breach at Equifax has dominated the news cycle, infuriating IT managers, security experts, legislators, and attorneys — and scaring consumers. It appears that sensitive personally identifiable information (PII) on 143 million Americans was exfiltrated, as well as PII on some non-US nationals.
Stupidity. Incompetence. Negligence. The unprecedented huge data breach at Equifax has dominated the news cycle, infuriating IT managers, security experts, legislators, and attorneys — and scaring consumers. It appears that sensitive personally identifiable information (PII) on 143 million Americans was exfiltrated, as well as PII on some non-US nationals. At the current rate of rainfall, when will your local reservoir overflow its banks? If you shoot a rocket at an angle of 60 degrees into a headwind, how far will it fly with 40 pounds of propellant and a 5-pound payload? Assuming a 100-month loan for $75,000 at 5.11 percent, what will the payoff balance be after four years? If a lab culture is doubling every 14 hours, how many viruses will there be in a week?
At the current rate of rainfall, when will your local reservoir overflow its banks? If you shoot a rocket at an angle of 60 degrees into a headwind, how far will it fly with 40 pounds of propellant and a 5-pound payload? Assuming a 100-month loan for $75,000 at 5.11 percent, what will the payoff balance be after four years? If a lab culture is doubling every 14 hours, how many viruses will there be in a week?
 When was the last time most organizations discussed the security of their Oracle E-Business Suite? How about SAP S/4HANA? Microsoft Dynamics? IBM’s DB2? Discussions about on-prem server software security too often begin and end with ensuring that operating systems are at the latest level, and are current with patches.
When was the last time most organizations discussed the security of their Oracle E-Business Suite? How about SAP S/4HANA? Microsoft Dynamics? IBM’s DB2? Discussions about on-prem server software security too often begin and end with ensuring that operating systems are at the latest level, and are current with patches. To think, the U.S. Secretary of State wants to send me money! Interesting that he’s using a gmail.com address for outgoing mail, a German email address for replies, and a phone number in the African country of Benin.
To think, the U.S. Secretary of State wants to send me money! Interesting that he’s using a gmail.com address for outgoing mail, a German email address for replies, and a phone number in the African country of Benin.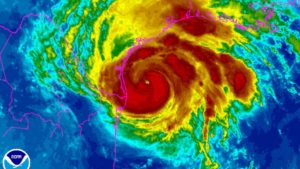 The water is rising up over your desktops, your servers, and your data center. Glug, glug, gurgle.
The water is rising up over your desktops, your servers, and your data center. Glug, glug, gurgle.